Best online collaboration tools
Work is moving online; these tools will help your team collaborate

The modern age and various unprecedented circumstances have pushed a large part of the global workforce to go mobile and/or start working from home. This transition has led to a rise in tools that allow these workers to accomplish their work tasks and remain in constant contact with their management, colleagues, and clients. Among the most popular ones have been online collaboration tools.
Not only have these tools helped facilitate normal communication among employees, but many of them have also provided handy collaboration options to better organise individual and group tasks, distribute them among individuals, keep track of their progress, and streamline the entire work process.
Without further ado, here are the best tools we discovered while scouring the online collaboration market.
The best online collaboration tools available
1. Microsoft 365
Document collab meets UC integration

REASONS TO BUY
- Robust and user-friendly apps
- Bundles for any user
- Microsoft Teams with UC
REASONS TO AVOID
- Somewhat limited collab features
Microsoft’s collection of cloud-based office tools, known as Microsoft 365 (formerly known as Office 365), is one of the most popular platforms of its kind, for more reasons than one. All the tools are easy to use, capable, and, most importantly - allow teams to collaborate in real-time on documents, from texts to spreadsheets to presentations, and more.
The appeal of Microsoft 365 is also in its accessibility on all major operating systems, including Windows, Mac, iOS, and Android. Some Microsoft 365 packages include Microsoft Teams, facilitating the integration of unified communications with the common office software.
Microsoft 365’s prices depend on whether you’re a personal or business user. The former starts at £5.99 a month, while the latter begins with Business Basic at £4.50 per user a month. From there, it gets somewhat more expensive with Apps for Business at £7.90 per user a month, Business Standard at £9.40 per user a month, and Business Premium at £16.60 per user a month. All of these prices are based on annual subscriptions, with Business Basic the more more economical option. While this option doesn’t include desktop versions of Office apps, it does include Exchange, OneDrive, SharePoint, and Teams services.
2. Slack
Handy collaboration tool that won’t eat up your resources

REASONS TO BUY
- Excellent service for free
- User-friendly and intuitive interface
- Isn’t heavy on resources
REASONS TO AVOID
- Free version only retains 10,000 messages
Slack is a popular collaboration tool that can be used on both desktop and mobile devices. Its primary function is exchanging direct messages and files between persons or inside a user group, expanded by the capability to organise chats into channels, say, for a specific project, department, company, topic, etc.
This tool stands out from the crowd thanks to its support for voice and video calling, be it through its desktop or mobile app, allowing for more direct contact when needed. There’s even your space inside the app, where you can draft messages, list your to-dos, or keep links.
This is in no way typical cloud storage but is very useful for sharing files with your colleagues (or keeping them on hand for yourself). While it lacks the cloud storage functionality, Slack can integrate with the likes of Google Drive, Box, Microsoft 365, and Dropbox. The best part? You won’t even notice it’s there if you’re not actively using it, as it doesn’t use up too much of your device’s resources.
You can use this awesome app for free with some limitations, such as the number of stored messages (up to 10,000), storage space, and so on, but no limitations on the length of time used. There are three paid plans - Pro at £5.25 a month, Business+ at £9.75 a month, and Enterprise Grid with customised pricing for extra-large businesses.
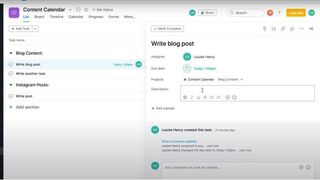
3. Asana
Proven track record in the industry
REASONS TO BUY
- Complete project overview
- Plenty of integrations
- Advanced features
REASONS TO AVOID
- Limited communication options
Asana is a well-known player in the collaboration field that has been offering its services for quite some time to the likes of Intel, Pinterest, TED, and Uber. There is a lot to like about Asana, as it allows companies to create and manage to-do lists for current and future projects, track their employees’ work assignments and progress, create reminders, set clear deadlines, send work requests, assign comments to posts, and more. Asana also has an integration with Microsoft Teams, Jira Server, and Zoom.
All the projects can be planned, visualised, and organised in a list, board, or calendar format, while a search option allows you to swiftly find any past task. You can get your hands on the Basic Asana package for free, with the only limitations on the file (100MB) and team size (15 members).
Paid plans include Premium at £9.49 per user a month (annual subscription), Business at £20.99 per user a month (billed annually), or a custom-priced Enterprise package. The Premium plan adds a timeline view, advanced search and reporting, forms, rules, milestones, and an admin console. Business introduces portfolios, custom rules builder, approvals, proofing, advanced integrations with Salesforce, Adobe Creative Cloud, Tableau, and Power BI, while the Enterprise pack throws in priority support, custom branding, data export, SAML, and SCIM.
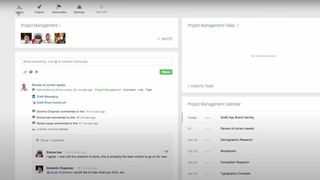
4. Podio
Collaboration goes fully mobile
REASONS TO BUY
- Integrates with plenty of third-party platforms
- Capable mobile options
- Fully customisable
REASONS TO AVOID
- Interface is a bit outdated
Podio is a great way to facilitate collaboration and communication among teams, allowing them to organise large projects and assign tasks. Employees can also take advantage of options like viewing ongoing projects’ status, file-sharing, and receiving feedback on current work. The platform can be used on desktop and mobile, and supports integration with services like Zendesk, Google Drive, Dropbox, and Evernote.
You can pick whether you want to be billed monthly or annually, with the latter option entailing some discounts. If you have up to five employees, you qualify for a rather limited yet free service that provides task management, apps, and workspaces.
The Basic plan, at £5.99 per user a month, throws in user management, as well as unlimited items and external users. At £9.33 per user a month, Plus will get you a light user role, automated workflows, and read-only access. Finally, the Premium package provides a full suite of advanced features at £15.99 per user a month. In addition to everything from the Plus plan, these include visual reports, contact sync, interactive sales dashboards, and advanced Workflow Orchestration by GlobiFlow. All of the prices mentioned are based on the annual pricing.
5. Ryver
Focuses on communication

REASONS TO BUY
- Beginner-friendly
- Handy extras
REASONS TO AVOID
- Some glitches in the app
Ryver focuses primarily on providing your business with an effective way of communication, accompanied by some surprising bonuses. One of them are filters for who can see your posts in the app and join your teams. You can also save your company’s posts in the Facebook-like newsfeed, for accessing them later.
The platform is available across all major operating systems (including Mac and Linux) and allows you to create countless teams inside those apps, categorise them, and set up chats with individuals or groups.
If you have up to 12 users, Ryver can be yours for just £57.45 a month (Starter), providing you with unlimited chat and file-sharing, task management, as well as video and voice calls. Increasing the number of users to 30 on Standard also increases the price to £107.40 a month, but also adds custom invite links. There's also a Medium Pack plan for over 30 user, offering the same functions and tools but for £3.89 per user a month. Finally, the Enterprise account, available via contacting sales, offers single sign-on (SSO), a testing sandbox, advanced team management, and premium support.
If you’re unsure about whether or not Ryver is the right collaboration solution for your team, there’s a 14-day free trial to see for yourself, but only for the Starter and Unlimited packages.
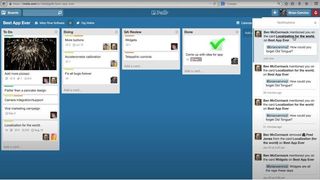
6. Trello
Simplistic collaboration app
REASONS TO BUY
- Free plan
- 2FA
- Easy to use
REASONS TO AVOID
- Lacks communication features
Trello is another popular collaboration and project management platform that can be installed on both desktop and mobile. Teams and tasks can be organised in the form of boards or lists, and within them, these tasks can be assigned to different people. Employees can also give each other feedback by writing comments to cards. Trello can be integrated with third-party apps including Slack, Google Drive, GitHub, and Evernote.
Its free version features unlimited personal boards, cards, and lists, but limits you to 10MB uploaded file size, 10 team boards, one power-up per board (like calendar, automation, custom fields, etc.), simple automation, 50 command runs per month, and two-factor authentication (2FA).
If you opt for its Standard package, it will cost you £4.16 per user a month (annual subscription) but will increase the maximum file size on 250MB, add advanced checklists, priority support, business-level security setting, unlimited power-ups, card repeater, calendar view, map view, voting, 100+ app integrations, unlimited team boards, board collections and templates, custom backgrounds and stickers, unlimited buttons, rule and scheduled commands, 1,000 command runs per team + 200 per user, email notifications, Google apps sign-on, advanced admin permissions, and more.
After this, the Premium plan offers all of the above plus dashboard, timeline, Workspace Table, Calendar and Map views, with unlimited Workspace command runs and a host of extra features for £8.33 per user a month, and is aimed at teams of up to 100.
Finally, the Enterprise package adds unlimited command runs, SSO for all SAML IdPs, power-up administration, organisation-wide permissions, attachment restrictions, public board management, and organisation-visible boards. You'll need to contact sales for exact pricing.
7. Flock
Solid communication-oriented work companion

REASONS TO BUY
- Free plan
- Excellent communication options
- Suitable for novices
REASONS TO AVOID
- Lacks task management features
Flock reminds of Slack in many ways - it facilitates messaging, audio and video calls, file exchange, the Do Not Disturb feature, essential productivity tools, and more, through free and paid service packages. It can also integrate with third parties like Twitter, Google Drive and Zoom.
The free plan is an excellent way to get smaller teams started, as it provides unlimited individual and group messaging, an archive for up to 10,000 searchable messages, 10 public channels, 5GB of total file storage space per team, single team admin, unlimited polls, reminders, notes, and third-party integrations, as well as individual video calls.
Going for the Pro package at £3.75 per user a month (billed annually) will remove the limitation on archived messages, increase the storage to 10GB per team member, add unlimited private and public channels, multiple team admins, group video calls for up to 20 participants, screen sharing, unlimited ToDos project management, and 24/7 priority support. This package comes with a 30-day free trial.
If you’re interested in the Enterprise plan, you'll need to contact Flock to get a quote (it can be done via live chat). With the Enterprise plan you can get 20GB per team member, Active Directory Sync with Microsoft Azure, real-time Active Directory Sync with OneLogin, Okta, and Ping, SSO, smart channels, unlimited announcement and auto-join channels, and 24/7 dedicated support.
Get the ITPro. daily newsletter
Receive our latest news, industry updates, featured resources and more. Sign up today to receive our FREE report on AI cyber crime & security - newly updated for 2024.
Sead Fadilpašić is a freelance tech writer and journalist with more than 17 years experience writing technology-focussed news, blogs, whitepapers, reviews, and ebooks. His work has featured in online media outlets from all over the world, including Al Jazeera Balkans (where he was a multimedia journalist), Crypto News, TechRadar Pro, and ITPro. Sead's experience also includes writing for inbound marketing, where he creates technology-based content for clients from London to Singapore. Sead is a HubSpot-certified content creator.





