Best cheap VPN
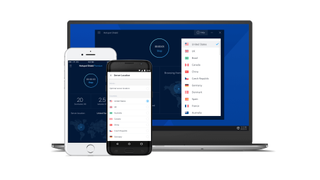
Demand for the best cheap VPN is always growing, and it's a clever move to try and get the most for your money. Here are our top picks

Having the best VPN (virtual private network) service these days is in no way overrated. After all, there are plenty of reasons to get one - governments and organisations spying on you or your business, blocking certain content based on your current location, or hackers trying to track you down and get access to your financial information.
Although there are some decent free VPN options out there, we highly recommend putting your trust into a paid-for service – and the cheap VPN services below deliver the goods without costing an arm and a leg.
Other than the price, the important things you should look at when choosing the best cheap VPN is the level of privacy and security they offer, as well as the range of platforms on which you can install and use them. Additionally, the ease of use is always a good trait for any VPN to have. Let’s take a look at the services that fit the description.
The best cheap VPN services right now
- Surfshark – the best-value VPN on the market
If you're looking for a cheap VPN that truly delivers the goods, then Surfshark may well be the provider for you. Its ever-increasing feature-set is a real match for premium providers, and at just £1.99 a month, it seriously undercuts them. - CyberGhost – an excellent alternative
Even cheaper than Surfshark, CyberGhost is available from a measly £1.70 a month. Don't be put off by that though – this cheap VPN delivers excellent security alongside dedicated streaming features that are virtually unheard of at this price. - NordVPN – the best-known VPN is great value
At £2.49 a month, NordVPN isn't quite as cheap as the above, but it offers class-leading privacy and security as well as excellent support and useful apps on tons of devices. If you want brand-name confidence, it's the one to go for.
The best cheap VPN providers available
1. Surfshark

Connect as many devices as you like for less than £2
SPECIFICATIONS
- Number of servers: 3,200+
- Server locations: 65
- Maximum devices supported: Unlimited
REASONS TO BUY
- Supports unlimited simultaneous connections
- Exceptionally cheap
- Lots of additional features
REASONS TO AVOID
- A bit basic for pro users
There’s a good reason Surfshark is the number one on our list - it will cost you less than £1.99 a month to have it if you take its two-year payment plan. This low price doesn’t mean there are many downsides to its service either. You get unlimited simultaneous connections, unblocked geo-restricted content, a solid number of servers, as well as some handy features like the Camouflage mode for added secrecy and the MultiHop feature routing your traffic through two VPN server locations.
The provider’s apps are available for Windows, Mac, Android, iOS, Linux, even Fire OS, while it also supports custom installation on game consoles, smart TVs, and routers. There may not be some super-advanced professional customisable features as in some, but consider you’re getting almost everything else.
Worried you won’t like it? Test it out during the seven-day no-charge period if you download its iOS or Android app, or the no-questions-asked 30-day money guarantee for all other platforms.
2. CyberGhost

Large server network and smart features list
SPECIFICATIONS
- Number of servers: 6,500+
- Server locations: 112
- Maximum devices supported: Seven
REASONS TO BUY
- Thousands of servers everywhere
- Superior features
- Extensive money-back guarantee
REASONS TO AVOID
- One-day Windows trial
CyberGhost has a longstanding reputation as one of the best VPN services due to the sheer size of its server network that counts over 6,600 units scattered all over the planet, support for torrenting and a long list of geographically limited content, as well as its wide platform support that includes all the popular players and then some.
And that’s not all. By signing up for its services, CyberGhost’s users are getting superior security and the possibility to use the VPN on as many as seven devices simultaneously. This number can be increased by setting it up on a router.
CyberGhost will give you an outstandingly fast and secure service for only £1.70 a month if you opt for its three-year subscription (you'll also get three extra months). If this is not enough to push you in its direction, then maybe its incredibly generous 45-day money-back guarantee will.
Also, CyberGhost will let you test out its services before you make the final decision. The trial period is one day for Windows and one week for iOS or Android.
3. NordVPN

VPN veteran with affordable and outstanding offering
SPECIFICATIONS
- Number of servers: 5,400+
- Server locations: 59
- Maximum devices supported: Six
REASONS TO BUY
- Wide server network
- Sturdy platform with pro features
- Unblocks everything
REASONS TO AVOID
- A bit more expensive than some
NordVPN is another big VPN name that prides itself on being among the cheapest in the industry. It provides superior services with a long list of advantages under the low price of £2.49 a month under the two-year pricing plan.
These features include support for all types of platforms, more than 5,400 servers, and strong security that is reinforced with the use of ‘Double VPN’ servers, directing your traffic through two different VPN locations, as well as the ‘Onion over VPN’ system that routes it over the Onion network.
In addition to the usual OpenVPN and IKEv2/IPsec protocols, the provider also uses modern, cutting-edge technology that is based on the new and fast WireGuard protocol, enhanced with a double NAT (Network Address Translation) system.
All users will be able to secure up to 6 devices at the same time, or more if they install NordVPN on a supported router, as well as get access to P2P and content available only in select countries (like Netflix, Facebook, BBC iPlayer, Amazon Prime, etc.).
You can test this all for yourself thanks to the no-questions-asked 30-day refund policy in place of a traditional free trial.
4. Hotspot Shield
Solid VPN with low price tag and limited free option
SPECIFICATIONS
- Number of servers: 1,800+
- Server locations: 80+
- Maximum devices supported: 5
REASONS TO BUY
- Free tier
- Simple to use
- High speeds
REASONS TO AVOID
- Not many streaming services supported
Pango’s Hotspot Shield has an advantage over many other cheap VPNs as it offers a portion of its services for free. The free tier includes 500MB of VPN traffic per day and one VPN location (US) but if this isn’t enough for you, there are two paid options at £6.99 a month and £10.49 a month under annual plans for premium and family packages respectively (£10.99 a month and £16.99 a month if you pay monthly). Also, Windows users can refer friends to get up to 10 weeks of the premium version for free.
This price will get you over 1,800 servers in 80+ countries, a solid range of tools such as the superior and fast proprietary Catapult Hydra protocol, and the possibility to protect up to 5 devices at the same time on a long list of platforms, including smart TVs and routers (removing the limit on simultaneously protected devices).
Many users will love its full support for P2P traffic exchange and geographically restricted services like Netflix US, Hulu, BBC, and others.
The provider is among those more generous with their money-back guarantees - giving you 45 days to ask for a refund if things go south.
5. Private Internet Access

Ideal for mobile devices
SPECIFICATIONS
- Number of servers: 29,600+
- Server locations: 77
- Maximum devices supported: 10
REASONS TO BUY
- High speeds
- Up to 10 simultaneous connections
- Huge number of servers
REASONS TO AVOID
- Slightly buggy Windows app
Private Internet Access (PIA) offers plenty under its low price tag of only £1.67 a month under the two-year subscription (you also get two extra months free). The offering includes apps for all the most popular platforms and extensions for Chrome, Opera, and Firefox.
Other advantages list all the classics - military-grade security and a handy kill switch feature which triggers a vibrating alert when activated on mobile. There is also a 24/7 live chat available.
With some guidance, the platform can also be enabled on certain routers and you can run VPN on as many as 10 devices at the same time. Additionally, it will allow you to download and upload large files via P2P clients.
That said, some downsides are present, such as the lack of access to the likes of Netflix and BBC iPlayer (despite the provider trying hard to change this) or a buggy Windows app. If that doesn’t make you any less interested, especially considering the price, you can give PIA a test ride during the risk-free 30-day money-back guarantee period.
Get the ITPro. daily newsletter
Receive our latest news, industry updates, featured resources and more. Sign up today to receive our FREE report on AI cyber crime & security - newly updated for 2024.
Sead Fadilpašić is a freelance tech writer and journalist with more than 17 years experience writing technology-focussed news, blogs, whitepapers, reviews, and ebooks. His work has featured in online media outlets from all over the world, including Al Jazeera Balkans (where he was a multimedia journalist), Crypto News, TechRadar Pro, and ITPro. Sead's experience also includes writing for inbound marketing, where he creates technology-based content for clients from London to Singapore. Sead is a HubSpot-certified content creator.





