Best printers for small business 2023: Quality, reliable, and easy-to-use printers for your business
Your small business needs a quality printer that won’t let you down - these are the best business printers around

Looking for the best printer for your small-to-medium-sized business? Look no further. We’ve rounded up the best small business printers from our selection of reviews, with prices ranging from a couple of hundred pounds all the way to breaking the four-figure mark.
Each product in our list links to a full review so you can learn more about each printer’s pros and cons in more detail, but we’ll provide the top-line information below so you can buy with confidence. When it comes to the best small business printers, we’re especially interested in things like resolution, speed and tray capacity, and you’ll find all of those highlighted in the table at the end.
What to look for in a small business printer
When it comes to printing, the needs of a small business will be different to those of a home user - even one that’s using it for work purposes. It's therefore important to really consider what type of printer your business needs.
For starters, small businesses will need a printer that can service multiple users, which means network connectivity is a key feature. Support for cloud printing will also be handy.
Similarly, running costs are more important than they would be for individuals, as small business printers will see greater print volumes over a longer period of time. For this reason, it’s worth considering either a tank-based inkjet or a laser printer, both of which can offer exceedingly good value for money in terms of consumables over their lifespan.
Serviceability may also be worth considering, depending on the structure of your internal IT operations. Organisations with a robust IT department will likely want printers that can be centrally managed and monitored, as well as something that makes it easy to troubleshoot printer problems and start repairs, whereas organisations that rely more on MSPs and third-party technicians may not need this as much.
Finally, if your print needs are going to include customer-facing marketing and promotional materials, you may want to invest in a more capable machine that can also handle tasks like larger A3 documents and good-quality photo printing. This will allow you to quickly generate impressive-looking marketing documents without needing to outsource the task to a third-party printing company.
FAQs for the best small business printers
Do I need a colour printer for my small business?
It may seem like getting a colour printer for your business is a no-brainer - after all, a colour printer can handle black and white documents while still giving you the option of colour prints when you need them - but there are actually some good reasons to deliberately choose a mono machine. For starters, you tend to get better quality for your money, as there’s a dedicated focus on one thing; this usually means higher quality and faster print speeds than you’d get with mono prints on an equivalently-priced colour machine, and it can also mean more features like duplexing and ADF that you may not get at a similar price point.
It also means better value on consumables, as most colour printers will still use a certain amount of their coloured consumables even when printing in grayscale, meaning you’ll need to order replacements more regularly. While having the capability to print colour documents is useful for a business, if most of your documents are intended for internal use, consider using mono printers for most of your fleet with one or two colour machines as backup.
How many printers does my small business need?
Digital documents may rule the roost these days, but paper still has a place even in a modern office. Some people simply prefer working with hard-copy documents, but there are also instances where you may need to physically sign and send off a form, or attach a tracking slip to a package. Every workplace should have at least one printer just in case of emergencies, but depending on the size of your organisation, you may need more than one.
How many you’ll need depends on a number of factors, of course, including the number of employees you have and how often they need to print, but you should also think about the physical space they’ll be occupying. If your office includes multiple floors, you may want to have a printer on each one, to minimise the time employees spend travelling to and fro.
Should I buy a laser printer for my small business?
Historically, laser printers have been the go-to machines for businesses wanting a sturdy and reliable option, thanks to lower running costs, faster speeds and excellent performance with mono documents. Lasers are no longer the unseatable emperors of business printing, thanks to the increasing sophistication of mid-range inkjet devices, but a laser printer may still be the best option for your small business.
Lasers are usually designed for high-volume document printing, so if you’re likely to be processing stacks of reports on a regular basis, this will be a faster option, and they’re often better value for money when it comes to consumables, too. Less moving parts can also mean better reliability, although this isn’t a given. The downside is that lasers are generally (although not always) larger, more expensive and less feature-packed than their inkjet cousins, and aren’t as versatile for things like photo or graphics jobs.
The best printers for small business
Canon Pixma TS8350
Best small business printer for general photo printing

| Pros | Cons |
| Excellent photo prints | Build quality could be sturdier |
| Quick print speeds | Row 2 - Cell 1 |
| Attractive design | Row 3 - Cell 1 |
If money is tight, then look no further than the Canon Pixma TS8350. This mid-range A4 inkjet is aimed at creative workloads but we found it to be more than capable of handling standard documents and reports as well. It comes in at under £150 after tax, despite supporting a range of exotic media types, and its a strong focus on delivering photo prints delivered bold and vibrant results in our tests.
For the low cost of entry, you simply can’t go wrong. Yes, we noticed the build quality is a touch flimsy in places, but it offers superb print quality. What’s more, in our speed tests, we measured an output of up to 13 pages per minute in black and white, or four pages per minute if you need a colour print, which is solid performance at this price. While there’s no automatic sheet feeder, if you need a machine to handle a combination of standout graphics and light document printing duties, then this should be near the top of your list.
| Technology | Inkjet MFP |
| Maximum print resolution | 4,800 x 1,200dpi |
| Cost per page | 3.4p/6.2p mono/colour |
| Connectivity | Wi-Fi, USB, SD-card reader |
| Speed | 13ppm mono/ 4ppm colour |
Price when reviewed: £100 exc. VAT
Read our full Canon Pixma TS8350 review for more information.
Epson EcoTank ET-5880
Best small business printer for overall TCO

| Pros | Cons |
| Great printing quality | Print speeds lag behind some rivals |
| Plenty of additional features | Expensive |
| Excellent value consumables | Row 3 - Cell 1 |
At the other end of the spectrum from devices like the cheaper Canon Pixma TS8350 is the Epson EcoTank ET-5880, with a cost that creeps just into four figures. However, if you print a lot, then it will pay for itself eventually: the EcoTank part of the name refers to its ink reservoirs, which you refill simply via bottles with no cartridges required. We found the process to be simple and straightforward, with no scope for spills, and our calculations show that it’ll cost you just 0.2p per mono page, or 0.8p for colour.
We were also particularly impressed with the quality of the results, and found text documents, colour reports and photographs were all produced with plenty of details and punchy, accurate colours. It offers plenty of flexibility too, with copy, scan and fax functionality alongside the standard printing. In our experience, its networking capabilities were top notch, with the ability to remotely print documents, and we could even protect top-secret files by requiring the entry of a four-digit PIN on the printer before the page is released. With a top speed of 25 pages per minute in our speed tests, it’s not the fastest machine we’ve ever seen, but it’s low running costs and plethora of additional features make this an easy recommendation.
| Technology | Inkjet MFP |
| Maximum print resolution | 4,800 x 1,200dpi |
| Cost per page | 0.2p/0.8p mono/colour |
| Connectivity | Ethernet, Wi-Fi, USB, fax |
| Speed | 25ppm mono/colour |
Price when reviewed: £1,076 exc. VAT
Read our full Epson EcoTank ET-5880 review for more information.
HP Color LaserJet Pro M255dw
Best small business printer for quick setup

| Pros | Cons |
| Automatic duplex printing | Colour printing could be better value |
| Fast, simple setup | No integrated scanner |
| Affordable price-point | Row 3 - Cell 1 |
If you’re on a tight budget and don’t care about scanning, then the HP Color LaserJet Pro M255dw is well worth a look, coming in at a hair over £200 before tax. Despite the name, we’d advise you to look elsewhere if the majority of your printing is in colour, as we found the shades were a touch oversaturated, with occasional flaws in the separation of colours. Black and white printing is outstanding, however, with text coming out crisp and sharp even at small sizes.
This printer’s biggest strength is how easy it is to set up; everything down to the toner cartridges comes preinstalled, and we were able to get up and running within mere minutes. Print speeds are good too; although it took the best part of a minute to warm up and start delivering pages, it quickly racked up speeds of up to 17ppm in our mono document test. Although you’ll get better value from an inkjet device, the high-yield toner cartridges offer prints at just 2.6p per black-and-white page, which is reasonable for a laser printer. The same can’t be said of colour costs, though, which work out at a rather pricy 13.5p per page.
| Technology | Laser |
| Maximum print resolution | 600dpi |
| Cost per page | 2.6p/13/5p mono/colour |
| Connectivity | Ethernet, Wi-Fi, USB |
| Speed | 17ppm |
Price when reviewed: £207 exc. VAT
Read our full HP Color LaserJet Pro M255dw review for more information.
Xerox C235dw
Best all-round small business laser printer

| Pros | Cons |
| Speedy mono performance | Low-capacity default toner |
| Well-rounded features | Slower colour speeds |
| Excellent quality | Row 3 - Cell 1 |
If you’re looking for a solid all-round laser MFP, the Xerox C235dw may well be worth a look. This printer, scanner and copier combo that may not completely oustrip the competition in any one area, but we found it balances its strengths and weaknesses well enough to provide capable performance across the board, including printing at a speed of 22ppm in our black and white document tests. We also observed excellent output quality, particularly with colour jobs in comparison to rivals.
We do have a couple of criticisms from our time with this machine; photo colours appear a touch too warm in places, mono photocopies need a bit of adjustment to maintain detail, and colour print speeds are slow compared to some rivals. You don’t get a fax for the £280 cost of entry either, and the default consumables it ships with are small in capacity - although even the larger 2,500-page alternatives still work out to a pricey 2.4p per page in mono, and 9.4p in colour. All told, however, it’s a solid business-class laser that ticks all the boxes for small businesses with modest needs.
| Technology | Laser MFP |
| Maximum print resolution | 600dpi |
| Cost per page | 2.4p/9.4p mono/colour |
| Connectivity | Ethernet, Wi-Fi, USB |
| Speed | 22ppm |
Price when reviewed: £280 exc. VAT
Read our full Xerox C235dw review for more information.
Oki B432dn
Best small business printer for fast mono printing

| Pros | Cons |
| Incredible speeds | Unappealing design |
| Affordable running costs | Limited feature-set |
| Fantastic quality | Row 3 - Cell 1 |
The Oki B432dn may be a boxy, unassuming-looking printer, but if you’re looking for fast, high-volume document printing then this diamond in the rough has you covered. A great example of a printer which does one thing incredibly well, the B432dn is mono laser model which chewed through our speed tests at a rate of knots. There’s no colour option, but it managed our black-and-white test document at 31.3ppm, and even managed a duplex graphic test at 14 images per minute.
It’s undeniably barebones in terms of additional features, with no scanner or fax capacity to speak of, but its functionality can be boosted with a £40 network adapter for Wi-Fi if you’re unhappy with ethernet connectivity, and with a 530-sheet paper tray if the default 250-sheet tray isn’t enough for you. Plus, we found that with the 12,000-page ultra-high capacity toner, running costs came to just 1.2p per page once the initial supply has been exhausted. To cap it all off, print quality is all but perfect.
| Technology | Mono laser |
| Maximum print resolution | 1,200 x 1,200dpi |
| Cost per page | 1.2p |
| Connectivity | Ethernet, USB |
| Speed | 40ppm |
Price when reviewed: £200 exc. VAT
Read our full Oki B432dn review for more information.
Canon Pixma Pro-200
Best small business printer for large-format photos

| Pros | Cons |
| Supports A3 printing | Bulky size |
| Phenomenal photo quality | Poor document performance |
| Row 3 - Cell 0 | Expensive consumables |
While it’s admittedly something of a niche product (even by the standards of small businesses MFPs) the Canon Pixma Pro-200 earns a place on this list by virtue of one thing: it’s the best photo printer we’ve ever seen by a considerable margin. We were absolutely flabbergasted by the quality of the images that this 14kg behemoth produced, including deep blacks, vivid colours and natural skin tones. If your business needs to print photographs, we’re confident you won’t find a desktop machine that does it better - and it even supports sizes up to A3. On the downside, however, we must point out that this printer is the virtual definition of a one-trick pony.
Don’t even think about using this for printing anything more than the occasional document, for example, as speeds are slow for both mono text and colour pages, coming in at 2.5ppm and 1.6ppm respectively. Ink costs are also fairly eye-watering, at 13p per page for both mono and colour. In all fairness, that’s calculated based on A3 prints, rather than the A4 size more commonly used by these kinds of devices, and it’s also a result of the eight ink cartridges that give the printer such superb photo results - but it’s still expensive. With that having been said, as long as you’re using it for its intended purpose, the results are well worth it.
| Technology | Thermal inkjet printer |
| Maximum print resolution | 4,800 x 2,400dpi |
| Cost per page | 13p/13.4p mono/colour |
| Connectivity | Ethernet, Wi-Fi, USB |
| Speed | 2.5/1.6ppm colour/mono |
Price when reviewed: £379 exc. VAT
Read our full Canon Pixma Pro-200 review for more information.
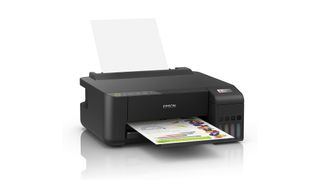
Epson EcoTank ET-1810
Best small business printer for everyday office printing
| Pros | Cons |
| Fantastic value for running costs | No scanning or copying functions |
| Good-quality photo prints | Middling speed and quality |
| Relatively compact footprint | Row 3 - Cell 1 |
While MFPs are all very well, sometimes all you need is simple, no-frills printing, and that’s what Epson’s EcoTank ET-1810 provides. It’s an ink tank printer, which means no cartridges to worry about, and we were particularly impressed with its keen value for running costs, which totalled an almost unbelievably low 0.29p per colour page, and a mere 0.16p per page of black text. For small businesses with heavy print workloads, this will handily offset the otherwise-high £158 pricetag.
Costs have been cut in other areas, of course, and Wi-Fi is the only added quality-of-life feature; there’s no scanning or copying capabilities, and no display for walk-up printing. Its print speeds of 8.8ppm in our mono document tests and 2.9ppm for colour pages wasn’t stellar, and neither was its quality (with the notable exception of photo prints), but we found both were capable enough to handle everyday office tasks, if not external marketing materials. It’s admittedly basic, but it does all it needs to do - and it’s excellent value in the long run.
| Technology | Inkjet printer |
|---|---|
| Maximum print resolution | 5,760 x 1,440dpi |
| Cost per page | 0.29p/0.16p mono/colour |
| Connectivity | Wi-Fi, USB |
| Speed | 8.8/2.9ppm mono/colour |
Price when reviewed: £158 exc. VAT
Read our full Epson EcoTank ET-1810 review for more information.
Canon MAXIFY GX7050
Best small business printer for long-term ink costs

| Pros | Cons |
| Good long-term value | Underwhelming colour performance |
| Strong mono performance | High outlay |
| Plenty of features | Row 3 - Cell 1 |
Some small businesses may struggle to justify the £447 list price of Canon’s monster MAXIFY GX7050, but for those that can stomach it, it’s packed with a range of features that you won’t find on other MFPs at this price range - including a 50-sheet ADF, duplex printing and scanning, multiple paper inputs and more. The result is a Swiss army knife of a machine that can handle just about anything a business can throw at it, with a maximum speed of just over 25ppm in our mono performance tests.
When we tested its colour speeds, they were only around 6ppm, and although we found black text was crisp and punchy, colour print quality wasn't exactly unimpeachable by our standards. This made up for by the low running costs which, like with many tank-based inkjets, are agreeably low. The initial capacity is high, but even once that's been exhausted, the cost per page works out at a mere 0.7p. This makes the MAXIFY GX7050 ideally suited to businesses with large requirements - although colour graphics may be a stretch.
| Technology | Thermal inkjet |
| Maximum print resolution | 600 x 1,200dpi |
| Cost per page | 0.7p mono/colour |
| Connectivity | Ethernet, Wi-Fi, USB |
| Speed | 25.4/6.1ppm mono/colour |
Price when reviewed: £447 exc. VAT
Read our full Canon MAXIFY GX7050 review for more information.

Best small business printer for affordability
| Pros | Cons |
| Excellent print quality | No ADF |
| Fantastic value | Noisy operation |
| Solid feature-set | Row 3 - Cell 1 |
Canon's inkjet printers have proven themselves to be outstanding options when it comes to the sheer quality of their results, and the PIXMA TS6250 is no exception. We found this robust yet compact MFP produced excellent results across mono text, photos and colour graphics - although the duplex print settings needed to be adjusted in order to get the best results for images. With a top speed of 12.7ppm, it didn't hold a candle to its larger stablemate the MAXIFY GX7050, but that's hardly surprising considering it costs barely more than £50 before tax. What is surprising is the amount of features that bought us; in addition to the double-sided printing mentioned above, there's a colour touchscreen, wireless connectivity and integrated flatbed scanner.
There's no ADF, and it's lacking more business-friendly features like fax or a front-mounted USB port, but it's an astonishing set of capabilities for the price. Value isn't as sharp in terms of ink cartridges, which work out to 2.8p per page for mono text and 8.6p for colour sheets when using the highest-yield options; that's a touch higher than we'd like to see, but for light to moderate printing, it's hardly enough to break the bank. The only other thing we noticed is that the TS6250 can be a little noisy in operation, but that's a small gripe that we're willing to overlook when the rest of the package gives you so much for so little.
| Technology | Inkjet MFP |
| Maximum print resolution | 4,800 x 1,200dpi |
| Cost per page | 2.8p/8.6p mono/colour |
| Connectivity | Wi-Fi, USB |
| Speed | 12.7/3.9ppm mono/colour |
Price when reviewed: £67 exc. VAT
Read our full Canon Pixma TS6250 review for more information
How we test small business printers
Like any hardware that we review, printers are put through a number of standardised tests to ensure comparable results across different products. We test black and white print speeds by running a 25-page document through the unit, timing how quickly it produces the first page after hitting print, and how long it takes to deliver the full job. These tests are also repeated at draft quality for inkjets.
For colour machines, we’ll also repeat these tests with 24 sheets of magazine pages, web pages and presentation slides, running the first ten pages again to test duplex printing where available. To test image quality, we look for any evidence of colour banding or fuzzy text in a series of colour photos, greyscale images and mono text documents.
Where printers also include the ability to scan documents, we’ll also test the quality by looking at the results from scanning an office document, a colour photo and a colour input target chart. To test the speed of its scanning operations, we’ll time a single photocopy, the speed with which it produces preview images and how quickly it delivers scans at varying resolutions.
For models with an ADF as well, we’ll copy a ten-page document in both mono and colour (if possible) to test its speeds, and if both printer and ADF functions are duplex-enabled, we’ll time how long it takes to process a ten-page double-sided document batch.
Get the ITPro. daily newsletter
Receive our latest news, industry updates, featured resources and more. Sign up today to receive our FREE report on AI cyber crime & security - newly updated for 2024.
After a false career start producing flash games, Alan Martin has been writing about phones, wearables and internet culture for over a decade with bylines all over the web and print.
Previously Deputy Editor of Alphr, he turned freelance in 2018 and his words can now be found all over the web, on the likes of Tom's Guide, The i, TechRadar, NME, Gizmodo, Coach, T3, The New Statesman and ShortList, as well as in the odd magazine and newspaper.
He's rarely seen not wearing at least one smartwatch, can talk your ear off about political biographies, and is a long-suffering fan of Derby County FC (which, on balance, he'd rather not talk about). He lives in London, right at the bottom of the Northern Line, long after you think it ends.
You can find Alan tweeting at @alan_p_martin, or email him at mralanpmartin@gmail.com.





