Tips for building your first business website
Building your first business website? We outline nine steps you should follow

Your small business website is your online calling card. You can use it to share information about your business, explain your products and services, and sell to your customers. But, if you're new to looking for the best website builder and building your first website, it can all seem a bit daunting.
Fear not. We've broken down each step you need to take so that you can get your website up and running, fast. Whether you're building a regular small business website or an ecommerce store, we've got you covered.
1. Choose the right building framework for your small business website
You have quite a few options when it comes to building your website, and our recommendation is to keep things as simple as possible. That means starting with a website builder like Wix, Squarespace, Shopify, or similar.
This will make your business website easier to manage, and you can get up and running quickly through the tutorials and examples they provide. The website builder you choose depends on your business needs:
Wix
Wix offers deep customisation and powerful tools. It offers multiple ways to create and edit your website, with plenty of templates and designs, but it does require a bit more study to learn how to use it effectively.
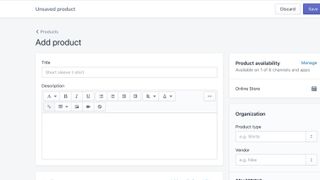
Shopify
Shopify is perfect if you're building an e-commerce store. It provides enormous functionality and third-party addons for getting your online shop up and running. If you're not selling online, other builders are probably better.
Squarespace
Squarespace designs beautiful-looking business websites. It's also optimised for mobile devices. Squarespace does have a learning curve, although it's easier to use than Wix.
Get the ITPro. daily newsletter
Receive our latest news, industry updates, featured resources and more. Sign up today to receive our FREE report on AI cyber crime & security - newly updated for 2024.
WordPress
WordPress gives you tons of customisation options, and there are plugins to do everything! But, the sheer number of things you can do with WordPress make it quite an intimidating tool.
2. Register a domain name
Decide on a name for your business, and see if it's available as a domain name for your website.
3. Think about how your users will interact with your site, and build the right pages and navigation structure

Your small business website needs to be fast, simple, intuitive, and easy to use.
- Think about how you want your customers to interact with and move through your website
- Understand the key information you'll need to provide, such as information about your business, the features and benefits of your products and services, contact details, pricing, etc
- Start planning out your navigation structure—you can do this on paper to begin with—as you want to make it as easy as possible for customers to access your site, find what they need, and complete a "call to action": getting in touch with you, buying a product, or some other desired activity
- Think about everything from your customer's perspective: ask, "is this simple?"; "Is this obvious?"; "Would I know where to click from here?"
- Wherever possible, avoid too many clicks—if it takes users more than two clicks to get from one section of the website to another, make changes to optimise the navigation
4. Try out some website builders, choose one, and read the tutorials
Discover the best website builder, and read through the reviews we've shared above. Then, it's time to roll up your sleeves and give them a try.
Each website builder we've mentioned comes with a free trial, so fire up each one and start creating a navigation menu and content.
5. Start experimenting and building your small business website
Messing around with these website builders is by far the easiest way to find out if they'll work for you. You'll get an idea of how they're designed, how the editor works, the templates you have access to, etc.
Here are some areas you'll want to experiment with:
- Setting up the menu and navigation
- Creating new pages for business information
- Setting up contact forms, so that people can get in touch
- Building out product and services pages to explain your business offerings
- Trying out different templates and how they affect the look and feel of your site
- Accessing your website through different devices, so you can see the experience of a mobile vs a desktop user
- Inserting images and videos for a more interactive experience
- Testing out ecommerce functionality like shopping carts
6. Create content yourself or get someone else to do it
Your small business website needs content. You can either create this content yourself, or hire someone else to do it. In many cases, hiring a specialised freelance is a good idea—they will be able to use their skills and experience to create effective and reliable content.
- Copywriters write compelling, persuasive copy that influences customers to buy; use them to create your static website pages (home, about, contact, etc.) and your product and service descriptions
- Content writers provide informational and educational content that helps to build relationships with your customers; use them for areas like blog posts, support guides, and lead magnets to attract customers
- Designers and visual artists create templates, images, and other visual media to help your website stand out; use them to help build your brand, logo, color pallet, illustrations, and similar areas
- You can source other freelancers for specific needs, like video makers for video guides, photographers for product images, SEO specialists to appear in search, and similar areas
7. Test out your small business website

You'll want to do some basic testing on your website before publishing it to the world.
- Once you've built your business website, get some fresh sets of eyes to look it over, as they'll be able to see things that "just don't look right": maybe the links aren't easy to click, or maybe there are images where there could be videos
- Read your website out loud, and note anything that doesn't sound natural
- See if anything looks off-putting or unprofessional; this could mean poorly-sized images, missing alt tags on images, errors in writing style, etc
- Make sure that all of your links work
- Test your website on different devices and browsers, then test it again
- Get ready for launch!
8. Launch!
It's time. You've chosen a website builder, read the tutorials, planned out your pages, experimented, hired some freelancers, put the content together, and tested your website.
Now, it's time to launch!
Follow your website builder's instructions for publishing a business website, and you'll be up and running. Once it's live, run a few more tests to make sure everything is running as expected.
9. Track how your business website is working and make improvements

When your business website is live and attracting traffic, track where it's coming from, how many people are visiting regularly, and what they're doing when they get to the site. You can use this data to make improvements.
You can tweak as needed to optimise your site. Maybe changing the tone of writing will increase conversations with customers. Maybe testing out different calls-to-action will lead to increased conversions. Whatever the case, measure how things are going, make some changes, measure again, and build in those improvements.
You'll see your small business grow and thrive!
Paul is a highly experienced professional writer who creates extensively researched, expert, in-depth guides across business, finance, and technology.
Boasting over 20 years of business experience working across large corporations, Paul started his own business in 2006. This gives him a unique, first-hand understanding of the challenges businesses and entrepreneurs face.
Paul loves the challenge of taking complex subjects and breaking them down so they are easily understood. He specializes in creating content spanning a variety of formats, including website copy, blogs, knowledge bases, white papers, support guides, tutorials, and in-depth articles.





