Best inventory management software
We round up the best inventory management software for small, medium and large enterprises

Whether your business is in manufacturing, retail, IT or any other sector, it's essential to keep on top of your inventory to make sure you can keep track of what's coming in, what's going out, what's being serviced and what you have in stock.
It's not just a simple case of tapping information into a spreadsheet. You need a system that can track shipments in real time, as well as allowing you to easily check stock where necessary.
Many inventory management tools are integrated into an enterprise resource planning (ERP) system, which will give you a full overview of your business resources. But we've also included some standalone inventory management tools in our roundup if you're not quite ready to make the jump to a full ERP just yet.
Asset Panda

Asset Panda hasn't just been designed for the manufacturing or retail industries. It works across a wide range of sectors, including IT, education, maintenance, hotels and facilities management to track hardware and software inventory across the entire organisation.
It's particularly useful for tracking the service life of a piece of equipment. For example, if you work in an IT department, you'll need to keep tabs on who's using which terminal, whether it's being serviced, if its maintenance is up to date and what condition it's in.
Asset Panda holds all of this information, with mobile terminals and barcode scanners available to communicate all of this data to the IT department. It uses GPS to track the equipment's location and supports photos of the products to show equipment is being maintained correctly.
Pricing: Customised for business
Get the ITPro. daily newsletter
Receive our latest news, industry updates, featured resources and more. Sign up today to receive our FREE report on AI cyber crime & security - newly updated for 2024.
ERP Mark 7
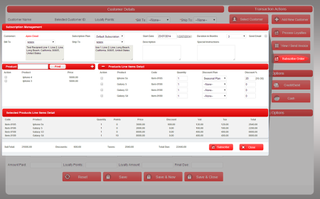
Aqxolt's ERP Mark 7 offers a full suite of services for manufacturing businesses, allowing them to keep track of their orders, inventory, finances and operations from one place. It's a modular platform, meaning businesses can pick and choose which operations they need to manage.
The inventory management module, for example, gives staff the opportunity to manage the job shop floor, putting the inventory first, with a barcode scanning system allowing them to simply scan and go.
Designed for small to medium-sized businesses, Aqxolt's ERP also offers asset management features, raw materials management to ensure you can continue to manufacture your products without a holdup, financial accounting with multi-language and currency support and customised reporting to present to key stakeholders.
Because Mark 7 operates from the cloud, everything is offered up in real-time, meaning you can get a true overview of the state of your business.
Pricin: Customised for business
Fishbowl Manufacturing
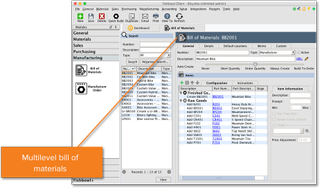
If you're already using QuickBooks to keep your accounts in check, Salesforce for your CRM, Amazon to sell through or one of the many other platforms to power your business, Fishbowl is the perfect integration to keep your inventory under control. With more than 30 third-party integrations, it definitely is one of the handiest inventory management tools out there.
It offers a full range of services required in the manufacturing industry, such as barcoding, asset management, raw materials management, cycle counting and customised reporting, all in-real time across multiple locations.
It's also an automation platform, enabling businesses to quote, order and purchase materials for their business so you can spend less time ordering and more time working on making your business processes more efficient.
Pricing: $4,395
Acumatica
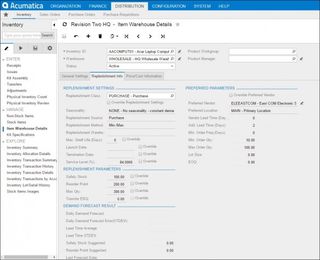
Acumatica's inventory planning tool helps you identify when you need to replenish supplies or when something's about to go out of date, making it a perfect option for the food and beverage industry. When an expiration date is approaching, it will prioritise the products with the least amount of shelf life left to minimise wastage.
Even for other industries, such as manufacturing, you can record serial numbers and implement cost tracking across a certain lot to discover which are the most profitable batches and why.
If you have more than one warehouse, you can see what's happening with stock levels in each location and with advanced item filtering, such as colour, size and style, which makes it easy to keep track of all stock levels.
Purchase orders are created autonomously and it'll give you the option of assigning them to specific vendors with the best price and delivery time for your business's success.
Pricing: On request
NetSuite Inventory Management
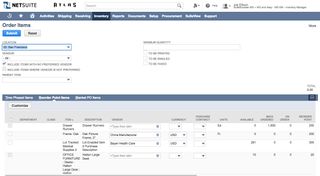
Oracle and NetSuite's inventory management platform automates the process of fulfilling orders and keeping count of your inventory within the familiar NetSuite OneWorld UI.
It offers you the opportunity to set your preferred stocking levels so you never run out of what you need, lead times for each product and re-order points to keep your supply chain running like clockwork.
Even in an automated system, it's vital you manually check over the levels too and this is made easy with Oracle NetSuite. The platform's Inventory Count allows you to categorise your products according to the number of completed transactions or value to see what's the most profitable and easily keep tabs on how much you have left.
Even if your products are distributed from multiple locations, you can keep track of where that inventory is and keep tabs on it across your entire warehouse network.
Pricing: From $99.00/month

Clare is the founder of Blue Cactus Digital, a digital marketing company that helps ethical and sustainability-focused businesses grow their customer base.
Prior to becoming a marketer, Clare was a journalist, working at a range of mobile device-focused outlets including Know Your Mobile before moving into freelance life.
As a freelance writer, she drew on her expertise in mobility to write features and guides for ITPro, as well as regularly writing news stories on a wide range of topics.




