Reviews
Latest reviews

Lenovo IdeaPad Flex 5i Chromebook Plus review: You can't beat this Chromebook Plus for value
By Stuart Andrews published
Reviews While not the strongest screen quality or performance, the Flex 5i Chromebook Plus gets most of the way there on a lower budget

Asus Vivobook Pro 15 OLED (N6506) Review: A high-quality all-rounder for a reasonable price
By Alun Taylor published
Reviews With a potent Nvidia GPU and superb 120Hz OLED display, the new Vivobook Pro is a superb do-it-all laptop that won't break the bank

Google Workspace Review
By Ross Kelly last updated
Reviews From free to enterprise, Google’s ever-popular productivity suite has a range of tiers and functions for all sizes of business

Lenovo ThinkPad E16 review: A dependable, low-cost laptop to supercharge small business productivity
By Alun Taylor published
Reviews The E16 is a decidedly unglamorous laptop but its solid keyboard and long battery life make it a great work machine

Trello review: An agile team workflow tool that feels familiar right away
By Nik Rawlinson published
Reviews The tactile project management suite has a focus on maintaining efficient teamwork and its most logical competition is a wall full of sticky notes

Broadberry CyberServe Ryzen RY1-104 review: A core-heavy Ryzen rack server at an entry-level price
By Dave Mitchell published
Reviews Broadberry presents a very affordable and more powerful entry-level alternative to Xeon E rack servers

Qnap TS-h1677AXU-RP review: Fast Ryzen-powered storage for SMBs
By Dave Mitchell published
Reviews A versatile and powerful rack NAS with excellent 25GbE performance and plenty of data protection features

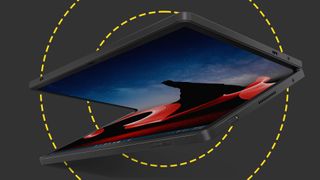
Lenovo ThinkEdge SE350 V2 review: Lenovo ditches the frills to provide serious firepower to those tight on space
By Dave Mitchell published
Reviews The SE350 V2 is a slim-line chassis that sports a more powerful D-2700 CPU and faster 3,200MHz TruDDR4 memory
Get the ITPro. daily newsletter
Receive our latest news, industry updates, featured resources and more. Sign up today to receive our FREE report on AI cyber crime & security - newly updated for 2024.